Privacy and Security Compliance Governance Defined
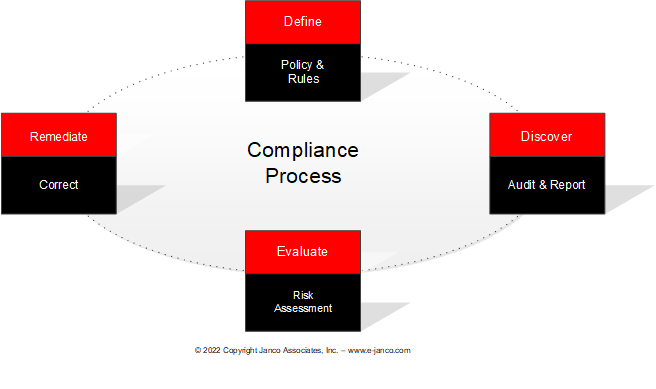
Privacy and security compliance governance necessary to meet mandated requirements is a multi-step process involving both IT and enterprise operations
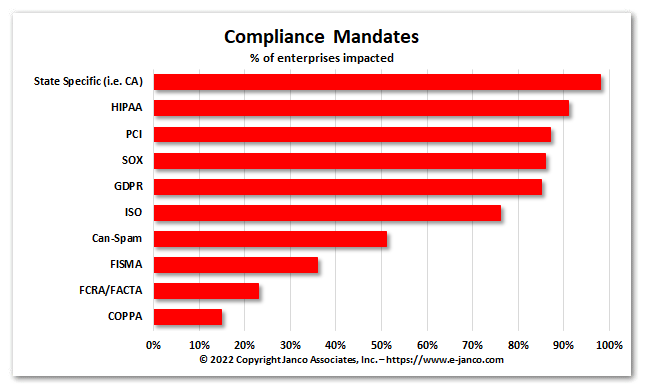
Data breaches, malware attacks, and mandated requirements are an everyday issue for organizations as the move towards e-commerce and blockchain architecture continues to take a larger portion of normal operations. With all of the additional demands this places on the technology processing functions, C-level executives are demanding that the CIO and CTO have in place tools to address these compliance and security issues.
The focus of the security and privacy compliance governance is on mandated requirements and ISO standards mandates. It is a five (5) step process.
Step 1 – Define where the enterprise is and the issues it faces
Define privacy requirements
Review existing privacy policies and statements and document how they compare with mandated requirements and ISO standards
Assess data subject rights to consent, use, access, correct, delete and transfer personal data
Discover and classify personal data assets and affected systems
Identify potential access risks
Define security requirements
Assess the current state of your security policies, identifying gaps, bench marking maturity and establishing conformance road maps
Identify potential vulnerabilities, supporting security and privacy by design
Discover and classify personal data assets and affected systems in preparation for designing security controls
Step 2 – Define what must be done
Keep reading with a 7-day free trial
Subscribe to CIO and IT Management Newsletter to keep reading this post and get 7 days of free access to the full post archives.